NIST 800-171 R3
Compliance Documentation
That Actually Works
Battle-tested documentation templates and implementation guidance for protecting Controlled Unclassified Information (CUI) in nonfederal systems. Best-in-class documentation structure provides the most comprehensive approach to being secure, compliant and resilient.
NIST SP 800-171 Revision 3 is the current standard. Organizations must transition from R2 to R3 - new ODPs, 17 control families, and expanded requirements are now in effect.
Key Changes in NIST SP 800-171 R3
NIST SP 800-171 Revision 3, finalized in May 2024, represents the most significant update to the standard since its original publication. Organizations transitioning from R2 should understand the scope of changes before attempting self-assessment or submitting a CMMC assessment.
The most impactful change is the introduction of Organization-Defined Parameters (ODPs) - which require organizations to specify tailored values for certain controls rather than accepting undefined defaults. This creates additional documentation obligations but also provides flexibility.
ComplianceForge publishes a free NIST 800-171 R3 Transition Guide that walks through every significant change in detail - highly recommended reading before beginning your compliance program.
17 Control Families (Restructured from 14)
R3 reorganized the control families, adding Planning (PL), System and Services Acquisition (SA), and Supply Chain Risk Management (SR) as standalone families.
→ New Families AddedOrganization-Defined Parameters (ODPs)
Many controls now require organizations to define specific values - timeframes, thresholds, frequencies. These must be documented in the SSP and justified.
→ Documentation RequiredSupply Chain Risk Management (SCRM)
SR is now a full control family with requirements for managing third-party risk, component provenance, and supply chain threat analysis.
→ New RequirementsEnhanced Assessment Objectives
R3 provides more granular assessment objectives per control, aligning to NIST SP 800-171A R3. Evidence requirements are more specific and explicit.
→ Increased SpecificityAlignment with NIST CSF 2.0 & SP 800-53 R5
R3 harmonizes more closely with NIST CSF 2.0 and SP 800-53 R5, including Govern function controls and enhanced privacy considerations.
→ Framework HarmonizationWhat Documentation Does
NIST 800-171 R3 Require?
NIST SP 800-171 R3 compliance requires specific documentation artifacts. ComplianceForge provides all required templates pre-mapped and ready to customize.
System Security Plan (SSP)
The cornerstone document describing how each security requirement is implemented. Required by CA.L2-3.12.4. Must include ODPs for all applicable controls.
Plan of Action & Milestones (POA&M)
Documents deficiencies, planned remediation actions and milestones. Required to demonstrate active management of security gaps to assessors.
Policies & Procedures
Documented security policies covering all 17 control families. Must address roles, responsibilities and frequency of activities with organization-specific tailoring.
Evidence & Artifacts
Technical evidence supporting each implemented control - configuration screenshots, scan results, training records, access review logs and system inventories.
Scoping Documentation
A documented assessment boundary defining which systems, people and facilities are in scope for CUI protection. The Unified Scoping Guide (USG) is the preferred method to scope sensitive and regulated data environments.
Supply Chain Risk Management
(SCRM) Plan - Now Required
Of all the changes introduced in NIST SP 800-171 Revision 3, none carries more weight than the addition of Supply Chain Risk Management (SCRM) as a standalone control family. This is not a checkbox exercise - a compliant SCRM program requires a formal, documented plan that addresses how your organization identifies, assesses and mitigates risks introduced by suppliers, vendors and third-party service providers.
The SCRM Plan must address the provenance of components and services throughout your supply chain, third-party assessment processes, and how CUI flows to and from subcontractors. Organizations that previously had no formal supply chain security documentation now face a significant documentation gap that must be closed to achieve compliance.
Both the NCP and CMMC Bundle 4 include pre-built SCRM Plan templates engineered to satisfy R3 requirements - saving organizations hundreds of hours of documentation development.
⚠ Compliance Gap Warning: Organizations transitioning from NIST SP 800-171 R2 that lack a formal SCRM Plan will have a significant POA&M finding. The SR control family cannot be satisfied with policy language alone - a documented SCRM Plan with named roles, processes and supplier assessment procedures is required.
Supply Chain Risk Identification
Documented processes to identify and categorize risks from suppliers, vendors, developers and system integrators providing components and services.
Supplier Assessment & Due Diligence
Formal procedures for vetting suppliers, reviewing their security posture and establishing criteria for acceptable supply chain partners handling CUI.
Component Provenance & Integrity
Controls to verify the authenticity and integrity of hardware and software components - addressing counterfeit, tampered or compromised supply chain elements.
Flow-Down Requirements to Subcontractors
Contractual and operational mechanisms ensuring CUI protection requirements flow down to subcontractors and third parties with access to sensitive data.
NIST SP 800-161 R1 - Cybersecurity Supply Chain Risk Management Practices for Systems and Organizations. The primary federal standard for SCRM program development.
DI-MGMT-82255A - DoD Data Item Description for the Cybersecurity Supply Chain Risk Management Plan. Required data deliverable for certain DoD contracts.
SCRM Plan templates included in:
NCP & CMMC Bundle 4 - aligned to NIST SP 800-161 R1 and DI-MGMT-82255A
NIST 800-171 Compliance Program
(NCP) – Battle Tested Solution
The NIST 800-171 Compliance Program (NCP) is purpose-built for NIST SP 800-171 R3 compliance - a “square peg for a square hole” solution with everything you need to demonstrate compliance with the standard. Battle-tested, efficient and proven effective for small to mid-sized organizations handling CUI.
Every required artifact is included: System Security Plan (SSP), Plan of Action & Milestones (POA&M), policies, standards, procedures and assessment tools - all pre-mapped to NIST SP 800-171 R3 requirements and the Secure Controls Framework.
Two Proven Paths to
NIST 800-171 R3 Compliance
ComplianceForge offers two documentation bundles for NIST SP 800-171 R3 compliance - choose the one matched to your organization’s size, complexity and CMMC requirements.
NIST 800-171
Compliance Program
NCP
The streamlined, purpose-built solution for organizations that need straightforward NIST SP 800-171 R3 compliance without unnecessary complexity. Everything you need - nothing you don’t.
- Complete System Security Plan (SSP) template mapped to R3
- Plan of Action & Milestones (POA&M) workbook
- All required cybersecurity policies & procedures
- NIST SP 800-171 R3 control mapping & ODPs
- Assessment guide and evidence templates
- CMMC Level 2 alignment documentation
- Streamlined for SMB efficiency - no bloat
CMMC Bundle 4
Level 3 / Advanced
CMMC Bundle 4
The most comprehensive NIST SP 800-171 and CMMC documentation package available - built for organizations that need enterprise-grade depth, cross-framework mapping and full program documentation.
- Everything in NCP, plus advanced CMMC Level 3 coverage
- Security, Compliance & Resilience Program (SCRP) full documentation suite
- Cross-framework mapping: NIST CSF, CMMC, ISO 27001 & more
- Comprehensive control narrative library
- Mature Governance, Risk & Compliance (GRC) documentation
- Supply Chain Risk Management (SCRM) artifacts
- Enterprise-scale evidence collection templates
Not sure which to choose? The NCP is the right choice for most organizations handling CUI under DFARS 252.204-7012 requirements. CMMC Bundle 4 is the better fit if you have a large, complex environment, pursue CMMC Level 3, or need enterprise-grade cross-framework coverage. Read the full comparison →
What Is NIST SP 800-171 R3?
NIST Special Publication 800-171 establishes the requirements for protecting Controlled Unclassified Information (CUI) in nonfederal systems and organizations. Revision 3 (R3), finalized in 2024, is the current version all organizations must comply with.
If your organization works with the federal government, especially the Department of Defense, and handles CUI under a contract, you are almost certainly required to implement NIST SP 800-171 R3 under DFARS 252.204-7012. This standard is also integral to the CMMC (Cybersecurity Maturity Model Certification) program, with the roadmap pointing to CMMC 3.0 Level 2 using NIST SP 800-171 R3 controls.
Compliance requires a documented System Security Plan (SSP), a Plan of Action & Milestones (POA&M), and evidence that security requirements are being implemented - not just claimed. That’s where documentation templates save significant time and cost.
What Is CUI?
Controlled Unclassified Information (CUI) is government-owned or generated information that requires safeguarding per law, regulation or policy - but is not classified. Examples include technical data, export-controlled information, privacy data and law enforcement sensitive information.
Scoping Failure = Compliance Failure
Many organizations fail to properly scope their CUI environment before implementing controls. Without a clear assessment boundary, you may over-scope the entire network or under-scope and miss critical systems. The Unified Scoping Guide (USG) provides the official scoping framework.
Self-Assessment vs. C3PAO
CMMC Level 1 requires annual self-assessments. Level 2 requires either annual self-assessment (for certain programs) or triennial third-party C3PAO assessment. Level 3 requires DIBCAC government-led assessments. NIST SP 800-171 R3 provides the technical baseline for all levels.
The SCF Advantage:
One Framework, All Requirements
The Secure Controls Framework (SCF) is a free, open-source meta-framework that maps over 100 laws, regulations and standards into a single unified control set. It is the most comprehensive cybersecurity & data privacy control catalog available.
ComplianceForge builds all its documentation on the SCF backbone - meaning your NIST SP 800-171 R3 documentation is already pre-mapped to CMMC, ISO 27001, NIST CSF 2.0, SOC 2, HIPAA and dozens of other frameworks. Implement once, satisfy many.
The SCF also provides the Secure Controls Framework Conformity Assessment Program (SCF CAP) for third-party assessments and certifications - giving organizations a single path to multi-framework compliance validation.
100+ Frameworks Pre-Mapped
NIST SP 800-171 R3, CMMC, ISO 27001, NIST CSF 2.0, SOC 2, HIPAA, FedRAMP, GDPR and more - all mapped in a single control framework.
Organization-Defined Parameters
R3 introduced ODPs requiring tailored values. ComplianceForge documentation includes ODP guidance with recommended values and rationale for all applicable controls.
Supply Chain Risk Management
R3 added SCRM requirements. SCF-based documentation includes supply chain controls, third-party assessment templates and flow-down requirement guidance.
Scalable from SMB to Enterprise
Whether you use the NCP for lean compliance or CMMC Bundle 4 for enterprise-grade documentation, both are built on the same SCF foundation and scale with your program.
All 17 Control Families
NIST SP 800-171 Revision 3 restructured from 110+ requirements in R2 to 97 core controls and 287 discrete requirements organized across 17 control families. Three families - Planning, System Acquisition, and Supply Chain Risk Management - are new in R3.
Access Control
Limit system access to authorized users, processes, and devices. Includes account management, least privilege, remote access controls and access enforcement.
Awareness & Training
Ensure personnel are aware of CUI security risks and are trained on applicable policies, procedures and practices to carry out their security responsibilities.
Audit & Accountability
Create and retain system audit logs to enable monitoring, analysis and investigation of unlawful or unauthorized system activity. Protect audit information.
Assessment, Authorization & Monitoring
Periodically assess security controls, develop and implement plans of action, connect to external systems through controlled interfaces and monitor continuously.
Configuration Management
Establish and maintain baseline configurations. Control changes, track inventories and restrict unauthorized software, firmware and hardware.
Identification & Authentication
Identify system users, processes and devices. Authenticate identities before allowing access. Includes MFA, password management and authenticator lifecycle.
Incident Response
Establish an operational incident-handling capability covering preparation, detection, analysis, containment, recovery and reporting to appropriate authorities.
Maintenance
Perform maintenance on organizational systems. Provide controls on tools, techniques, mechanisms and personnel that perform maintenance activities.
Media Protection
Protect system media containing CUI, both paper and digital. Limit access, sanitize or destroy media before disposal or reuse. Control transport.
Physical Protection
Limit physical access to systems and equipment to authorized individuals. Protect and monitor the physical facility and provide physical access audit logs.
Planning New in R3
Develop, document and periodically update system security plans that describe security requirements and controls. Includes rules of behavior and security architecture.
Personnel Security
Screen individuals prior to authorizing access. Ensure CUI is protected during and after personnel actions such as transfers and terminations.
Risk Assessment
Assess risk to operations, assets and individuals. Scan for vulnerabilities periodically and remediate findings. Includes supply chain risk considerations.
System & Services Acquisition New in R3
Allocate adequate resources for information security. Employ system development life cycle practices and secure engineering principles across acquisition processes.
System & Communications Protection
Monitor, control and protect communications at external boundaries and key internal boundaries. Implement network segmentation and protect CUI at rest and in transit.
System & Information Integrity
Identify, report and correct information and system flaws. Provide malicious code protection, monitor systems and alerts, and protect against unauthorized code execution.
Supply Chain Risk Management New in R3
Establish a supply chain risk management program. Identify and address supply chain threats, assess suppliers, and manage risks associated with CUI in the supply chain.
What Makes ComplianceForge
Documentation Different
The documentation market is flooded with templates that look compliant but fail under actual assessment scrutiny. ComplianceForge documentation is built differently - engineered on the Secure Controls Framework (SCF), the most comprehensive cybersecurity control catalog available.
Every control narrative is written to align with NIST SP 800-171A R3 assessment objectives - meaning your SSP documentation is specifically designed to satisfy what assessors actually test for, not just nominally reference the requirement.
The SCF cross-framework mapping means your NIST SP 800-171 documentation simultaneously satisfies CMMC Level 2, NIST CSF 2.0, ISO 27001 and other frameworks - reducing audit fatigue and supporting multi-framework compliance with one set of authoritative documentation.
“Good documentation does not just describe what you do - it proves you understand why you do it and demonstrates it at scale. Every ComplianceForge template is written with the assessor’s questions in mind.”
Written for Assessors
Control narratives aligned to NIST SP 800-171A R3 assessment objectives - not generic descriptions, but evidence-ready implementation statements.
Complete Documentation Suite
Not just policies - SSP, POA&M, procedures, standards, controls catalog and evidence templates all provided in a coherent, integrated package.
Multi-Framework by Design
SCF-based mapping means one documentation investment covers NIST 800-171, CMMC, ISO 27001, NIST CSF 2.0, HIPAA and more simultaneously.
ODP Guidance Included
R3 Organization-Defined Parameters are addressed throughout with recommended values, acceptable ranges and rationale for each ODP-enabled control.
Battle-Tested in Real Assessments
ComplianceForge documentation has been used in real CMMC and DIBCAC assessments. It’s not theoretical - it’s proven effective under real scrutiny.
Immediate Delivery, License to Customize
Delivered electronically and licensed for customization. Start your compliance program the same day without waiting for consultants or custom development.
Hierarchical Cybersecurity Governance Framework (HCGF)
The Hierarchical Cybersecurity Governance Framework (HCGF) is the ComplianceForge reference model that defines how cybersecurity and privacy documentation components are structured and interconnected. This comprehensive framework identifies the primary documentation components necessary to demonstrate evidence of due diligence and due care, addressing the inter-connectivity of policies, control objectives, standards, guidelines, controls, risks, procedures and metrics.
The Secure Controls Framework (SCF) fits into this model by providing the cybersecurity and privacy controls an organization needs to implement. This hierarchical approach is what separates ComplianceForge documentation from generic templates that lack structural coherence and fail under assessment scrutiny.
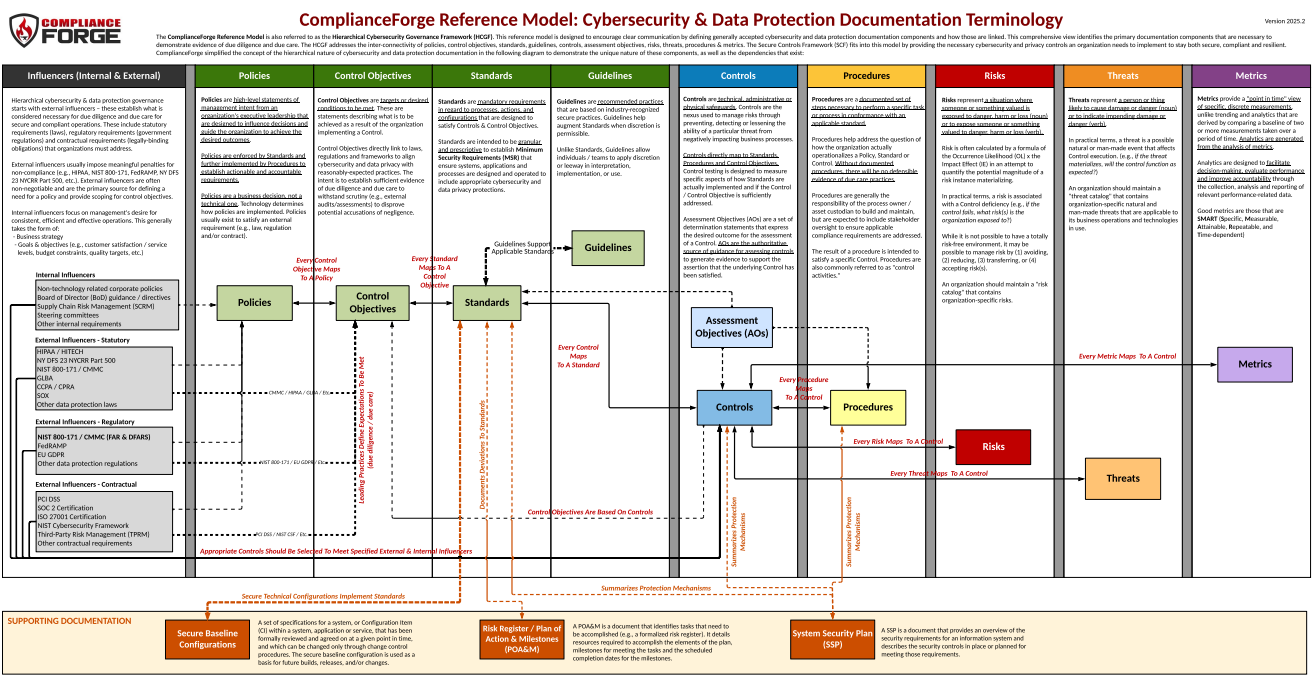
Clear Documentation Hierarchy
Defines the unique nature of policies, standards, controls and procedures, along with the dependencies that exist between them, so every document serves a distinct purpose.
Evidence of Due Diligence and Due Care
Provides the structural foundation assessors expect to see, demonstrating that your organization understands not just what controls exist, but how governance flows from strategy to operations.
Interconnected Governance Components
Maps the relationships between policies, control objectives, standards, guidelines, controls, risks, procedures and metrics into a single coherent model.
SCF Integration
The Secure Controls Framework plugs directly into the HCGF, providing the cybersecurity and privacy controls needed to stay both secure and compliant across 100+ statutory, regulatory and contractual frameworks.
NIST 800-171 R3 Across
Regulations & Standards
NIST SP 800-171 R3 doesn’t exist in isolation. Understand how it fits into the broader regulatory and compliance landscape.
CMMC 2.0 (Level 2 & 3)
NIST SP 800-171 R3 is the technical foundation for a current CUI program. While not all 97 core controls and 287 discrete requirements in 800-171 R3 map to CMMC 2.0 Level 2, the roadmap is for CMMC 3.0 Level 2 to use NIST SP 800-171 R3 controls. Organizations pursuing CMMC certification should now start work on demonstrating full 800-171 R3 compliance.
DFARS 252.204-7021DFARS 252.204-7012
The primary DoD contract clause requiring NIST SP 800-171 implementation for contractors handling CUI. Requires an SSP, POA&M and a SPRS score submission to the Supplier Performance Risk System.
DoD ContractorsGSA CIO-IT Security 21-112
GSA’s procedural guide requires federal contractors processing CUI on non-federal systems to comply with NIST SP 800-171. Applies across GSA contract vehicles and supply chain participants.
GSA ContractorsITSP.10.171 (Canada)
The Canadian Communications Security Establishment (CSE) published ITSP.10.171 to guide Canadian organizations protecting specified information for non-Government of Canada systems - closely aligned with NIST SP 800-171.
Canadian IndustryExecutive Order 13556 & 32 CFR Part 2002
The executive order establishing the CUI program and its implementing regulation define what constitutes CUI and who must protect it - providing the authority for NIST SP 800-171 applicability.
CUI Governing AuthorityNIST CSF 2.0 & SP 800-53 R5
NIST SP 800-171 R3 was updated to harmonize with NIST CSF 2.0 and SP 800-53 R5. SCF-based documentation bridges all three, enabling organizations to satisfy multiple NIST standards simultaneously.
Framework HarmonizationFrequently Asked Questions
What is NIST SP 800-171 Revision 3?
NIST SP 800-171 R3 is the current version of the standard for protecting Controlled Unclassified Information (CUI) in nonfederal systems, finalized in May 2024. It expanded from 14 to 17 control families and introduced Organization-Defined Parameters (ODPs) requiring organizations to tailor specific control values.
Who is required to comply with NIST 800-171?
Any organization with a DoD contract that involves CUI under DFARS 252.204-7012. GSA contractors per CIO-IT Security 21-112. Canadian contractors handling specified information under ITSP.10.171. Any entity in the DoD supply chain that may encounter CUI through contract performance.
What changed from R2 to R3?
R3 added three new control families (Planning, System Acquisition, Supply Chain Risk Management), introduced ODPs for control tailoring, enhanced assessment objectives, and aligned more closely with NIST CSF 2.0 and SP 800-53 R5. ComplianceForge’s free R3 Transition Guide documents all changes in detail.
What is the difference between NCP and CMMC Bundle 4?
The NCP is purpose-built for NIST SP 800-171 R3 compliance - ideal for smaller to mid-sized organizations seeking efficient, focused compliance. CMMC Bundle 4 is the enterprise-grade option including the full Security, Compliance & Resilience Program (SCRP) with broader cross-framework coverage, more depth and better suited to complex, large-scale environments.
Does NIST 800-171 R3 satisfy CMMC Level 2?
No. CMMC 2.0 Level 2 is essentially NIST SP 800-171 R2. That does not address all 97 core controls and 287 discrete requirements in NIST SP 800-171 R3. If you achieve full CMMC 2.0 Level 2 compliance under NIST SP 800-171 R2, that leaves a significant gap with NIST SP 800-171 R3 compliance.
What are Organization-Defined Parameters (ODPs)?
ODPs are placeholders in certain NIST SP 800-171 R3 controls where organizations must specify their own tailored values - such as the frequency of access reviews, password complexity requirements or session timeouts. These values must be documented in your SSP and justified based on organizational risk decisions.
What is the Secure Controls Framework (SCF)?
The SCF is a free, open-source meta-framework that harmonizes 100+ cybersecurity laws, regulations and standards into a single comprehensive control set. ComplianceForge builds all documentation on the SCF, meaning NIST 800-171 documentation simultaneously maps to CMMC, ISO 27001, NIST CSF 2.0 and more.
What is the SPRS score and how does it relate to 800-171?
The Supplier Performance Risk System (SPRS) score is a self-assessed score from -203 to 110 representing your NIST SP 800-171 compliance posture. Contractors must submit this score under DFARS 252.204-7019. A well-documented SSP and POA&M are essential to calculating and defending your SPRS score.
Get NIST 800-171 R3 Compliant -
The Right Way
ComplianceForge provides the only documentation built on the Secure Controls Framework - proven in real assessments, mapped to every major framework, and designed to satisfy NIST SP 800-171 R3 compliance at any scale. Choose the NCP for streamlined SMB compliance or CMMC Bundle 4 for enterprise-grade coverage.